Due Date: May 3, 2024
Assignment
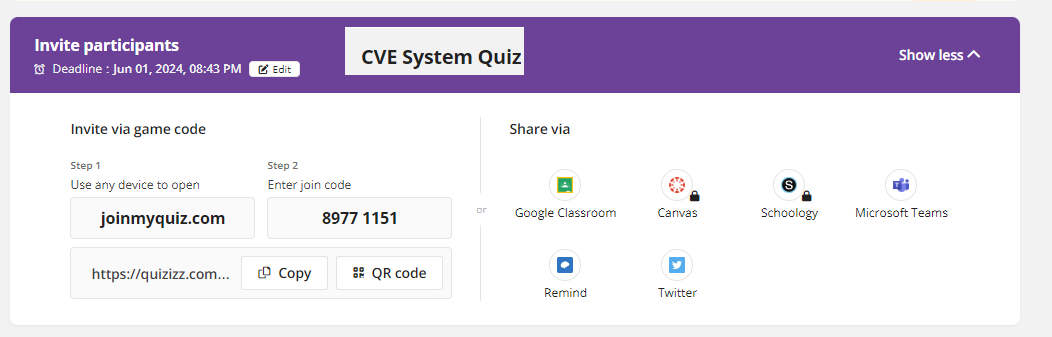
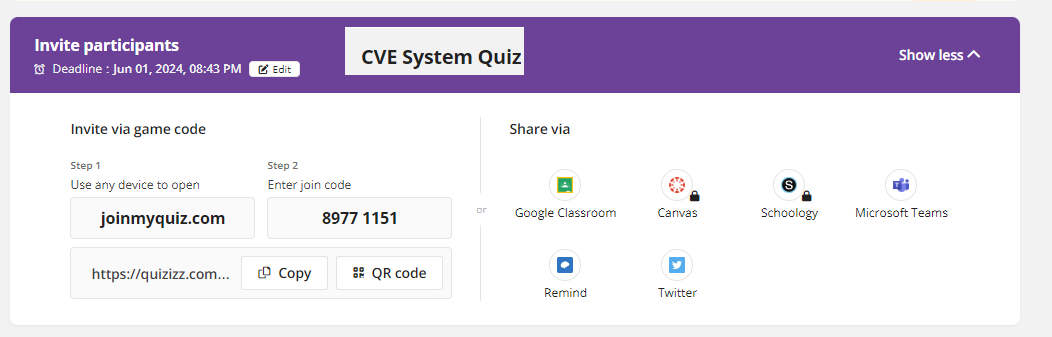
-Practice Quizizz for CVE System Vulnerabilities
Click here to practice the quizizz.
https://quizizz.com/join?gc=89771151

Due Date: May 2, 2024
Unit 3 - Data Safety and Best Practices
3.1.1 - System Vulnerabilities
in cybersecurity refer to weaknesses or flaws
in a computer system
that can be exploited by a threat actor, such as a hacker,
to gain unauthorized access or cause harm to the
system.These vulnerabilities can exist
in software, hardware, or organizational processes.
They may include outdated software, unpatched
security holes,weak passwords, or configuration errors.
Identifying and mitigating such vulnerabilities is
critical for maintaining the security and
integrity of information systems.
Regular updates, security audits, strong
authentication procedures, and employee training are
some measures to protect against these vulnerabilities.
• Identify System Vulnerabilities
Click here and read about the lesson.
Click here and read the lesson Guide.
Copy the document found below into a google document.
Answer the questions in your google document.
Highlight the answer in yellow.
Name the the google document "Lastname - 3.1.1 - System Vulnerabilities"
Update Lastname to your last name.
Title: "3.1.1 - System Vulnerabilities".
Modify the Standard heading with your information.
Amanda Success (Period 9)
Monday December 25, 2023
Seat 99 (Grade level 13)
Cyber Fundamentals
The CVE worksheet.
Due Date: May 3, 2024
Assignment
-Practice Quizizz for CVE System Vulnerabilities
Click here to practice the quizizz.
https://quizizz.com/join?gc=89771151
-Locate your Cyber Range Passwords below by seat number.
Cyber Range Sign on ids and passwords (Period 1)
Click here and get your id and password.
Click here for your cyber range.
https://apps.cyber.org/login
-Using Linux and the python interpreter
If you have forgotten how to boot up your Kali Linux machine and run python.
Click here for full instructions.